
Your Privacy. Our Priority.

Technical Surveillance Countermeasures (TSCM): Protect Your Privacy & Confidential Spaces
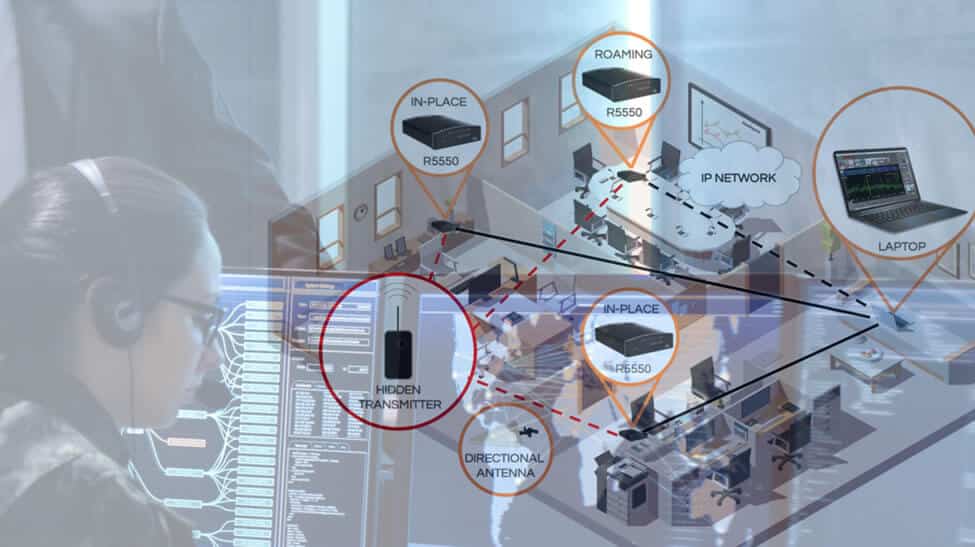
When confidentiality matters in offices, residences, vehicles, or travel, regular security isn’t enough. Hidden microphones, cameras, GPS trackers, or covert transmitters can compromise private conversations, sensitive data, and personal safety. Our TSCM services make sure that doesn’t happen.
TSCM Services We Provide:
- Bug sweeps and hidden-device detection: we search for and identify hidden recording or surveillance devices, then neutralize them.
- Signal and electronic sweeps: detecting unauthorized transmissions or suspicious signals that might indicate covert surveillance.
- Physical-space inspections: including rooms, furnishings, wiring, and infrastructure to uncover hidden cameras, wiring-taps, or improperly secured areas.
- Custom deployments: from corporate offices and conference rooms to private residences, vehicles, travel lodgings, and temporary venues.

Why Perform a TSCM Sweep:
- Ensure privacy and confidentiality for meetings, personal discussions, or sensitive operations.
- Protect against espionage, unauthorized surveillance, data leaks or reputational risk.
- Provide peace of mind for high-value clients, executives, families, or any party handling sensitive information.
- Reduce risk and liability when security of communications, discussions or assets is critical
The Samaritan Difference:
- Experienced, trained specialists who are equipped to handle technical and physical counter-surveillance inspections.
- Flexible services: one-time sweeps or scheduled inspections depending on your risk profile and needs.
- Discreet and professional execution: respecting privacy and operation confidentiality.
- Adaptable coverage for homes, offices, vehicles, travel locations, or any environment where privacy matters.


Learn More
