Listening & Recording Devices: Are You Being Bugged?
Copyright Samaritan Protective Services, Woodbridge, Virginia
Have you had a private conversation with a confidant only to have details emerge later? Discussed a new technology or product your firm is developing, then learn a competitor is releasing a very similar or identical item? Does nothing seem to stay within the confines of four walls and your activities are always known? As surprising as it may sound, you may be bugged!
History Of Bugs:
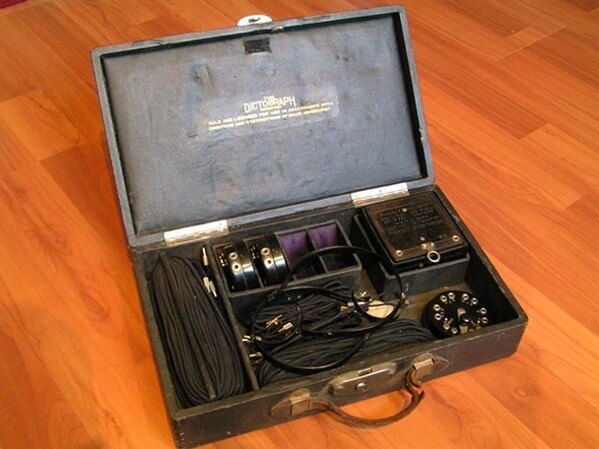
Despite being considered a high-tech form of espionage (which they can be), technical surveillance has been occurring for some time. One of the earliest known listening devices to receive a patent in the U.S. was the Dictograph. This device placed a microphone in one location and a remote listening post equipped with a phonograph for recording. The Dictograph dates to 1906.

Adversarial nations have been conducting technical surveillance for decades. It was a staple intelligence collection tactic during the Cold War and continues to remain a viable option today. Corporate espionage is a very real and dangerous problem for many sectors, especially Critical Infrastructure. The loss of proprietary information, trade secrets, research and development can lead to significant security and economic damage.
Means of Deployment:
There are three main categories of illicit device deployment:
- Plug & Play: Quickly and easily plug into a power source after positioning and leave. Designed to transmit information over a specific frequency, such as to a cell phone.
- Leave & Retrieve: Contains onboard limited power supply, such as with a digital recorder and is designed to be left in a designated area to be surveilled, then retrieved at a later date for data collection.
- Hardwired: The most complex and difficult to detect, as these devices are typically embedded within appliances, have sustained power supply, require planning and expertise to deploy. Typically placed in areas that frequent conversations such as conference and break rooms. Are often disguised as fire alarms, radios, TV’s, clocks and many other common office or home devices.
Types of Devices:
Through the years, listening and recording devices have been improved significantly, both in their covert nature and ability to capture detailed audio and video. They are also easily obtainable, overall inexpensive and easily deployed with minimal skill and training. Additionally, some usually innocent devices may be used to conduct illicit surveillance activities. While by no means an exhaustive list, here are a few types of listening, monitoring and recording devices.
- Two-Way Radios & Baby Monitors: Easily obtainable, cheap and simple to deploy. With a constant power supply, these can transmit indefinitely or until discovered.
- Digital Recording Device: Very affordable and newer models can record for days and have voice activation, increasing battery life. Must be physically retrieved for exploitation.

- Remotely Activated Cell Phones: This requires specialized software (apps), physical access to the phone and additional technical skills, however it is completely possible to turn someone’s phone into a remote listening device. Activation of cameras, interception of live phone calls and video messaging is possible with today’s technology.
- Laser Microphones: These are extremely powerful and prohibitively expensive listening devices that bounce a specialized laser off glass (such as in an office building), detect the vibrations from conversations and send back to the operator for conversion into audio and further exploitation. Extremely rare in the private sector.
- Covert Audio/Video Cameras: These devices are small, wi-fi capable, inexpensive and easily obtainable from spy shops, eBay and Amazon. They are often designed to be hidden inside other objects such as stuffed animals, tissue boxes, cell phone chargers or other electronic devices. These can also be hidden on people, such as lapel pins, buttons, writing pens and even shoes.


What is TSCM?
Technical Surveillance Countermeasures (TSCM) is the systematic and comprehensive detection, identification and potential neutralization of illicit recording, listening or monitoring devices. Proper TSCM is conducted by trained and industry certified technicians with some of the most advanced detection equipment available. These TSCM specialists have years of operational experience, hands-on technical training and subject matter expertise in the field.
Buyer Beware:
There are countless online spy shops and specialty stores that offer low priced, cheaply made and mostly ineffective “bug detection” gear. These devices often have flashing lights, gimmicky names and detect very limited frequency bandwidths only inches away. Do not trust your privacy to toys. Detection of illicit devices requires numerous specialized (and expensive) pieces of equipment that detect certain types of devices, radio frequency bands, infrared and even microwave transmissions. From non-linear junction detectors to spectrum analyzers or near field detection receivers and other specialized equipment, the correct devices must be used to comprehensively detect, identify and neutralize covert technical surveillance devices.



Samaritan Protective Services has the trained personnel, operational experience and assets to meet the unique needs of clients nationally and globally. If you or your organization is in need of a quality and comprehensive technical surveillance countermeasures program, contact us today. Samaritan’s team of professional risk managers will discuss our portfolio of risk management solutions and how a strategic partnership with us can provide value and peace of mind.
Contact Samaritan Protective Services today for a free consultation.
Samaritan Protective Services is located at 3985 Prince William Parkway, Suite 203, Woodbridge, VA 22192. Founded in 2015, we specialize in Executive Protection, Corporate Security, Workplace Violence Protection, Bodyguard, Armed Security, Close Protection, Security Consulting, House of Worship, Dignitary Protection, Celebrity Protection, Event Security, Private Investigations, TSCM, Armored Car, Surveillance, Counter surveillance, Secure Transportation, VIP Protection Services, Intelligence and Risk Advisory, Emergency Response and more.





